
Have you decided you need a better Perimeter Security plan?
Attending the 13th Annual NCS4 Conference & Exhibition?
Rest easy and feel confident your guests are safe from
vehicle attacks.
Ask Concentric at the NCS4
Conference & Exhibition on
June 28-30 in Orlando, FL.

Chris Truss
Business Development Team
Perimeter
Security Solutions
Done-for-You!

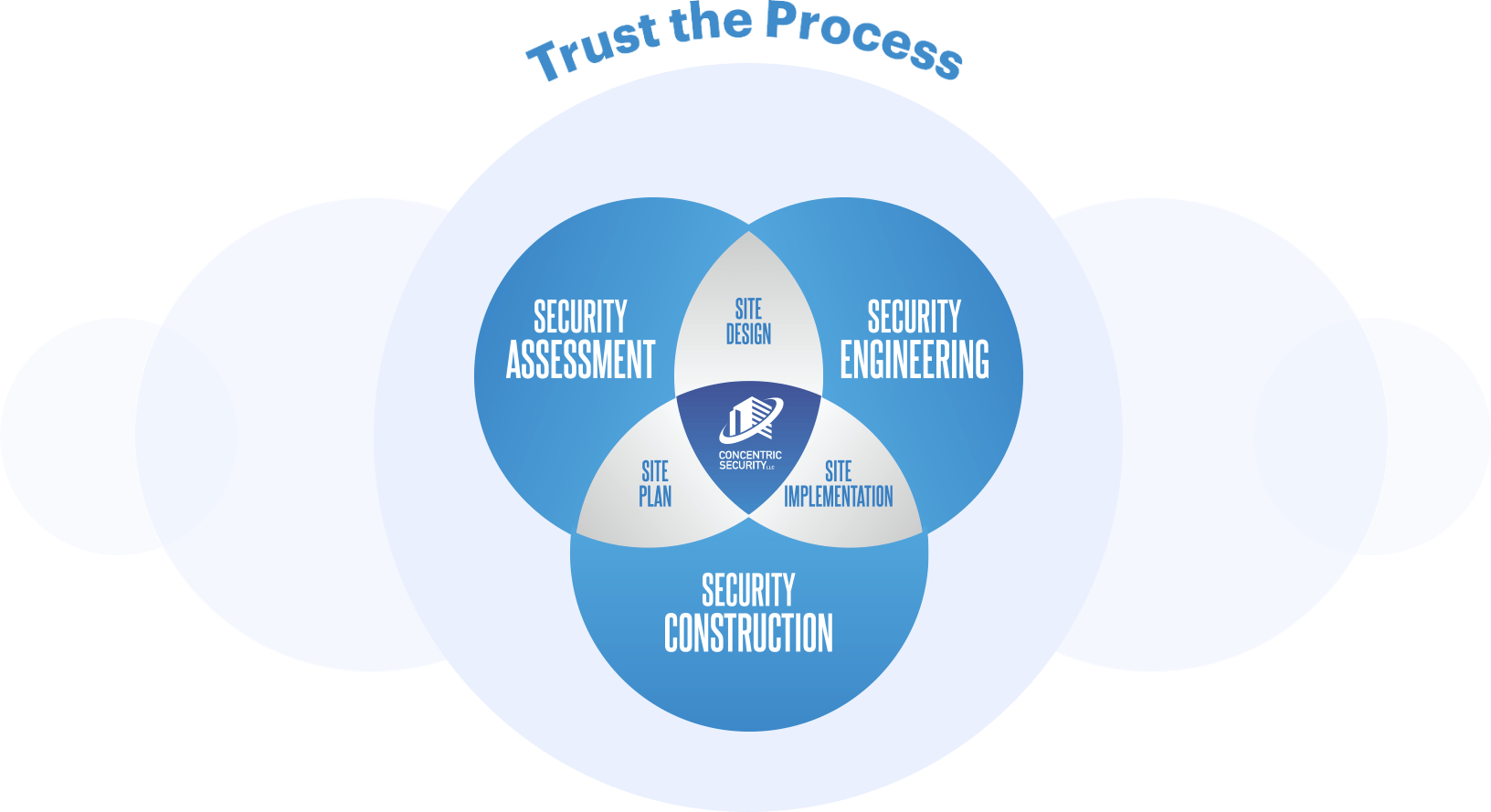
At Concentric Security, we know your venue is unique. You have different security needs, challenges, stakeholders and technology requirements. This is where we shine.
As the industry leader in perimeter security, we’ve seen it all and know there is no one-size-fits-all solution.


Let’s Talk!
Contact us here and get a shortcut to the answers you need.
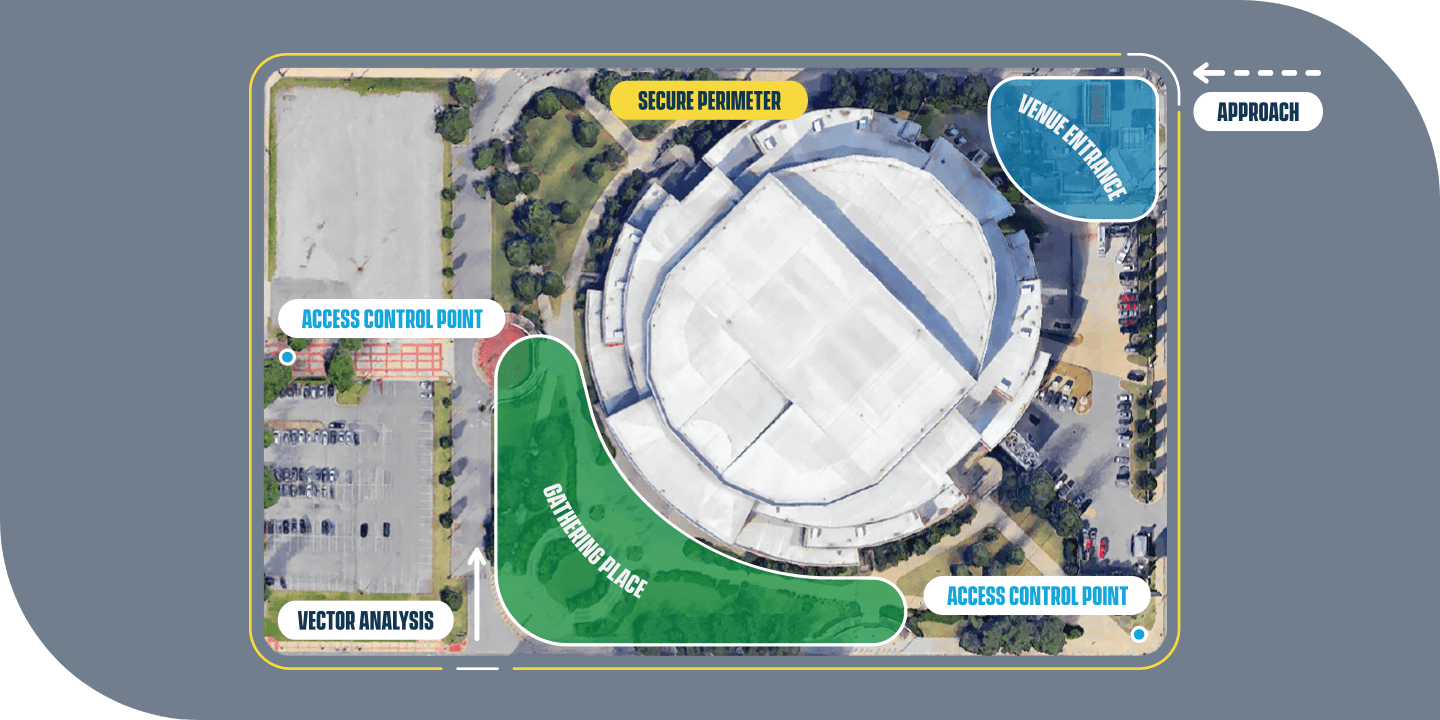
Assessment
- Site Characteristics
- Vulnerability Assessment
- Vector Analysis
- Blast Analysis
- Threat Verification
- Stakeholder Input
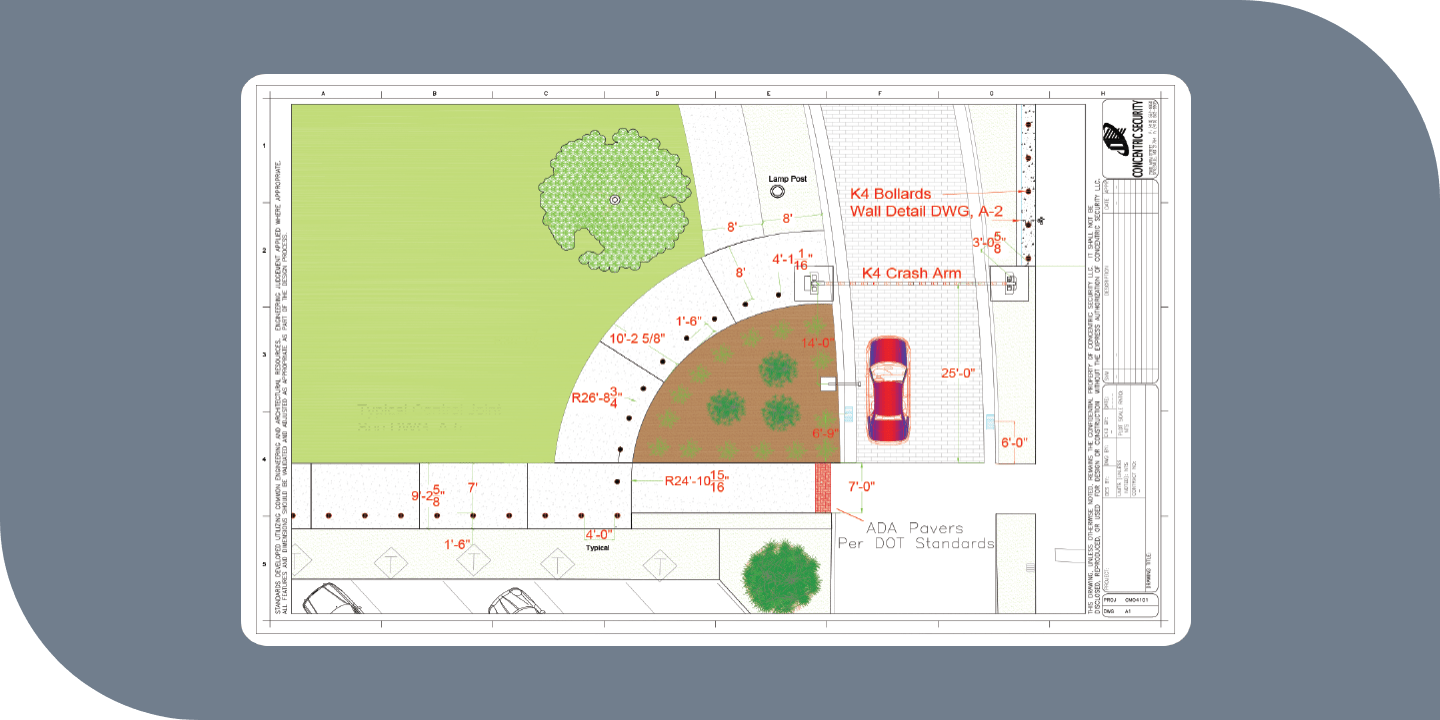
Engineering
- Technology Selection
- Civil Review
- Existing Infrastructure
- Underground Encumbrances
- Drainage
- Layout Design
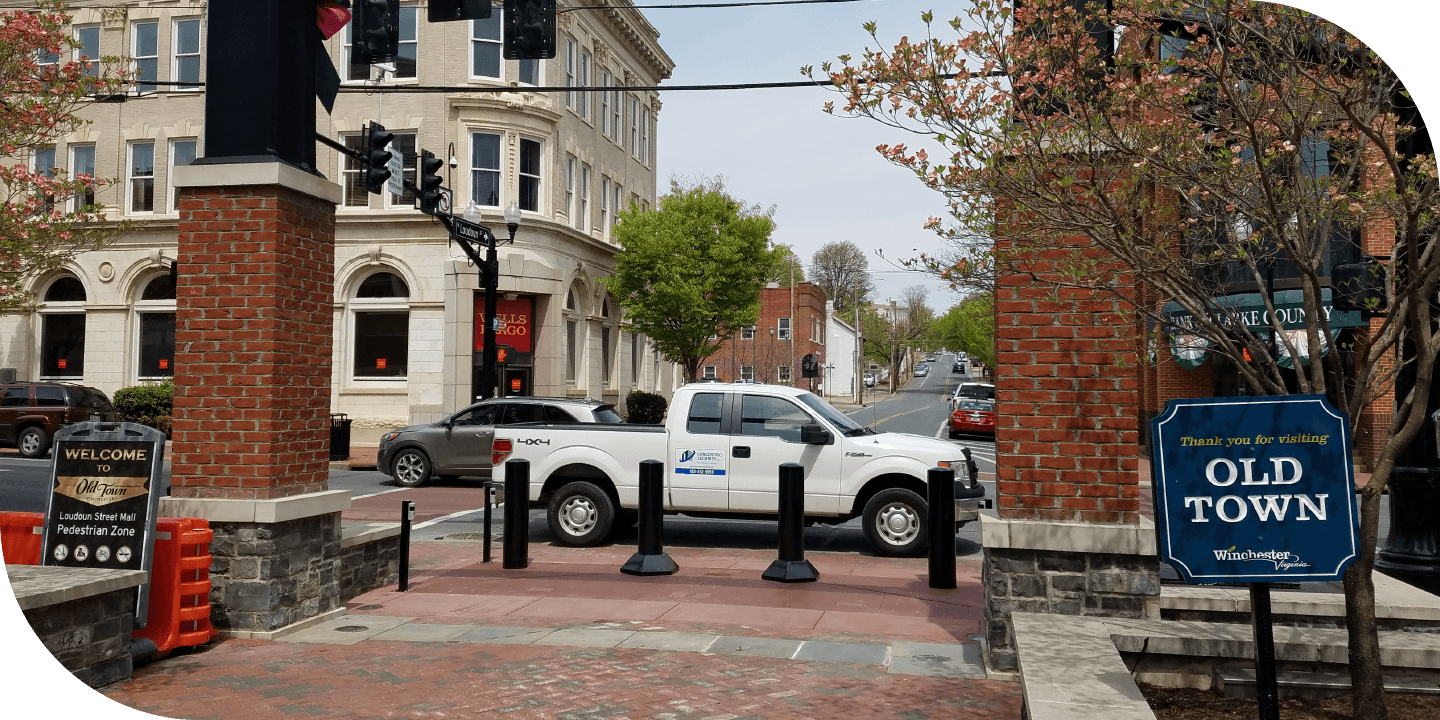
Construction
- Submittals
- Material Procurement
- Installation
- Verification Testing
- Training
- Warranty & Service
Learn MoreConcentric Security Newsletter - October 2021
Click here to learn more about how the Concentric Security Process can help you rest easy
and feel confident your guests are protected against vehicular attacks.
Unique
Perimeter Security Solutions



Shallow Mount Solutions
Perimeter Access Control










Concentric Security on the 12th annual NCS4 Conference and Exhibition November 9-10 | Phoenix
Concentric Security is excited to attend the 12th annual National Sports Safety and Security Conference and Exhibition
on November 9-10 in Phoenix. Schedule a meeting to discuss your unique perimeter security plan and how
you can feel confident your guests are safe.